
We connect the IoT and provide security for data and devices
With our leading IoT solutions, we ensure the global connectivity and efficient lifecycle management of IoT devices. Starting with production, continuing with the lifetime of the product, and ending with the deactivation of the device. Our experienced global teams assure that G+D is both partner and pioneer in tackling the three key IoT challenges: connection, secure transmission, and analysis. Since the beginning of the Internet of Things, our company has worked with the largest and most well-known companies in the market. We address all stakeholders in both the enterprise and consumer IoT ecosystems including operators, device makers, OEMs, module and sensor makers, and semiconductor providers.
The market is ready for massive IoT
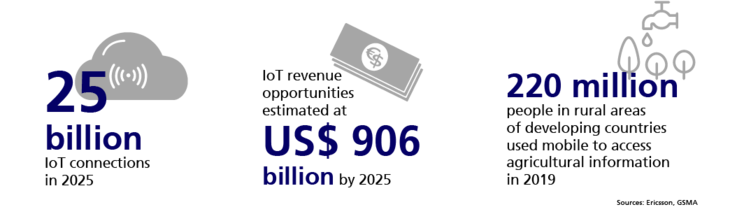
The IoT is growing rapidly, and the arrival of 5G will propel this growth dramatically. In the near future, billions of devices, machines, and systems will be connected to the internet in real time. Identifying, linking, and protecting them efficiently, while complying with national and international rules and legislations, will be the central challenge of this entire ecosystem.
From sensor to enterprise IoT platforms: we connect things
We offer secure, robust solutions for any enterprise that operates networked devices in the world of the IoT. G+D solutions connect, manage, and secure the IoT.
Staying competitive in the complex IoT ecosystem
With the integration of IoT technology, enterprises face a monumental challenge. How can digital security be applied to processes that have never been digitalized or networked before?
Businesses compete in a challenging environment where big data, IoT, and cloud computing rule. They also operate in complex environments that involve a large number of players. Many small and medium-sized enterprises find it especially difficult to enter the market under these circumstances.
To minimize complexity, IoT players are seeking to reduce the number of suppliers and partners they interact with. They look to work with just a small group of trusted suppliers who can provide them with flexible and securely connected ready-to-use modems.
Businesses want to ensure instant and uninterrupted interconnectivity. Customization is another important basic requirement. You need to be able to tailor a device both in the factory and in the field – whether it’s for a sensor or a smart building. No matter if your solutions are for managing enterprise integrations or other platforms, they must undergo complex certification processes and fulfill certain standards.
The trend is crystal clear
- The number of cellular IoT devices connected to platforms are booming
- Sensors, smart devices, industrial operations, and numerous other applications make this growth exponential, instead of linear
- We will all be affected by this colossal IoT machine, which in its interconnected state can be considered the biggest machine ever to exist
- Ensuring security and data integrity is fundamental. With increasing complexity, however, this becomes increasingly difficult
- G+D is here to help – as your one-stop-shop for your IoT needs
The best interoperable IoT solution on the market
We offer a standard one-stop solution based on hardware roots of trust that bring eSIM (eUICC), security service, and connectivity. By providing access to 600+ networks in 185 countries worldwide, backed up by satellite connectivity as a fail-safe, our solutions comprise flexible and secure connectivity for devices and IoT solutions for small and midsize OEMs, enterprises, and service providers.
G+D also offers a modular portfolio of eSIM-enabled IoT solutions for secure device connectivity, lifecycle management, and cloud computing connection. Our best-in-class support and years of experience help you integrate and scale products globally.
We manage the lifecycle of components that are relevant for trusted connectivity, data protection, and integrity. Our IoT packages offer the best interoperable systems on the market. They provide you with maximum flexibility and assure independent scalability. We make sure that IoT modems work globally, in all networks – so that both module and device makers can reduce costs and inventory.
Highlights
Introducing the world's first secure Integrated SIM
G+D incorporates satellite-based IoT connectivity for true global coverage
Global coverage in G+D's IoT service offering will be ensured in the future by their partnership with satellite-based IoT connectivity providers. Whenever a terrestrial cellular connection is unavailable, roaming to a satellite network is automatic. This will enable G+D to offer users of its IoT services true global coverage.
Analyst report

The Definitive Guide to 5G with Satellite Communications
This analyst report from Beecham Research looks into the benefits of integrating 5G with satellite for the IoT, and the different industries that will benefit from this development.
More insights into IoT solutions
Get in touch
If you have any questions about our end-to-end business solutions or about our SecurityTech company, seek expert advice, or want to give us your feedback, our team is here to support you, anytime.












