Our solutions drive the pulse of mobile digital life
Our digital life involves an incredible number of devices. It relies on massive amounts of mobile data that must be transported securely at high speeds over a vast number of networks. No doubt, mobile network operators (MNOs) are the key players in this connected, mobile society. In fact, more than 800 MNOs operate across an extensive variety of networks. G+D supports them to manage risks and, at the same time, exploit opportunities. The technologies in this area are evolving rapidly – and sometimes even change radically. No matter what, security and establishing trust in the market are always top priorities for all players. G+D offers solutions such as eSIM management so you can ideally position your business – for today and tomorrow.
We put you in control of mobile services
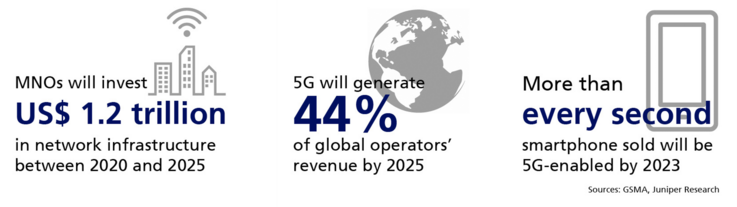
MNOs have to answer many questions that will determine the future: How can I grow my subscriber base in saturated markets? How can I monetize 5G and the opportunities of the IoT across markets? What strategies will enable me to manage disruptive market players who are offering new business models?
Reduce complexity and increase flexibility
With our proven solutions, you can create a straightforward and convenient customer experience. We provide trusted and secure end-to-end solutions comprising classic pluggable SIMs, embedded SIMs (eSIMs), embedded operating systems (eOS) for smart card controllers, lifecycle management services, and SaaS solutions with the highest service levels.
Trust in our experience – we know where to go
The number of subscribers and access points is continuing to rise. Also, users have more and more mobile devices that require access – whether we’re talking about human subscribers or connected IoT devices.
But that's not all:
- The virtualization of networks and wireless technologies are creating new infrastructures.
- Digital customer journeys have developed from a “nice to have“ to a “must have.”
- MNOs are required to provide agile connectivity and identity services.
End-to-end solutions for your complete customer journey
Today’s connected society is built on mobility and connectivity. In this arena, conditions change quickly and sometimes radically. As a network or virtual network operator, you are ideally capable of updating and adapting your business model for efficiency and profitability. With our solutions, you can redefine customer journeys from the ground up. And in so doing, you can offer more ubiquity and simplicity. With our support, you can transform the customer journey and become an end-to-end service provider, gaining the ability to manage every single aspect of an end user’s digital and mobile life. Our role is to develop, configure, deploy, connect, and manage billions of mobile devices securely – every second of every minute.
Highlights

G+D scores #1 vendor for eSIM Management
G+D is officially again a Kaleido Champion for its eSIM subscription management solution. The motivation from Kaleido reads: “G+D remains a leading player on the market for eSIM Subscription Management capabilities and counts a significant number of both eSIMs under management in addition to devices deployed with its eUICC OS. Over the past year, it has highlighted innovative work in the context of SGP.32 as well as SGP.42, while the overall solution is supplemented with a considerable range of professional services capabilities and VAS”.
More insights into our solutions for MNOs
Get in touch
If you have any questions about our end-to-end business solutions or about our SecurityTech company, seek expert advice, or want to give us your feedback, our team is here to support you, anytime.